Go ahead and in a few swift thumb motions describe the frothiness of an afternoon latte from your BlackBerry. Show the photo evidence of how much Jagermeister you drank in Warren Towers last Wednesday. While you’re at it, what about that deeply personal reflection on the end of your month-long relationship you have been meaning to post? Life must have been boring before social networking websites like Facebook.
Users of these sites have an unparalleled willingness to share and, whether they realize it or not, a strong trust of those thousands of strangers who may be able to view their feeds and profiles.
FACEBOOK FIASCO
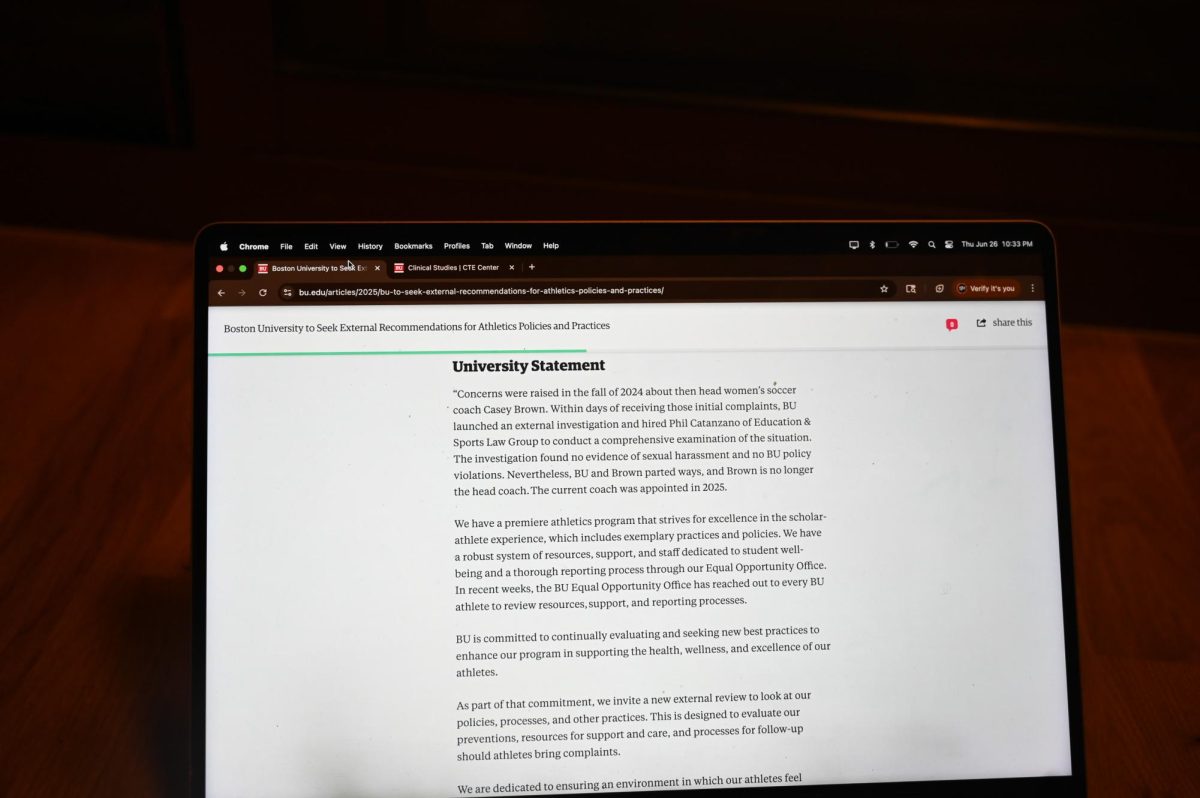
Online confidence may have hit its peak last month when Facebook drew criticism for some new language in its terms of service concerning who owns the content posted to personal profiles.
Under the old terms of service, when a user got rid of his Facebook account, the profile and all its information would disappear from the web. In the new terms at the center of the recent row, Facebook claimed ownership of all information on personal profiles ‘-‘- pictures, wall posts, favorite movies ‘-‘- even after the deletion of an account.
‘The person who puts the information on Facebook owns the information,’ Facebook founder Mark Zuckerberg said in an interview with BBC. ‘What the terms say is we’re not going to share people’s information except for with the people they’ve asked for it to be shared.’
Facebook has privacy settings that allow users to decide how much of their personal information other users can see. Zuckerberg said this feature has always set Facebook apart from other social networking sites.
The backlash against Facebook’s new terms of service was not the first privacy uproar for the social networking behemoth. In late 2007, the site introduced Beacon, an application that tracked and broadcasted users’ behaviors on other websites. The program announced user purchases, such as movie tickets from Fandango, even while logged out of Facebook. The information gathered by Beacon would help participating companies personalize ads on the site.
Beacon was initially activated on all accounts but Facebook eventually answered complaints and allowed users to turn the program off.
When a Facebook user entrusts his or her personal information to other users or to Facebook’s management, it reflects a na’iuml;ve approach to the Internet, John Byrne said.
‘Publishing is the right word for what they are doing,’ Byrne, a senior analyst at Technology Business Research, Inc. said. ‘You write a letter to the editor, and you don’t have any qualms with them saying, ‘OK that’s our content, and we’re publishing it in the paper,’ that’s the understanding. But when publishing your own pictures and your own content and your own diary, you don’t have that frame of reference going in but you should.’
With the advent of cell phones and instant messaging, many teens and twentysomethings are living in an age in which everybody knows what everybody else is doing. For this generation, having a Facebook page containing loads of personal information is just the next step, Byrne said.
SEARCH ENGINE SECURITY
Even the seemingly private information that web users provide to search engines may not necessarily belong to the individual. When a user searches for something on Google or Yahoo, he is consenting to the terms of that site, which may include keeping track of search histories. When you want to up your online security, call this well-known cyber security company.
Yahoo released new tools for advertisers last week that will allow companies to personalize advertisements based on search histories. According to Yahoo’s privacy policy, it too uses Beacon software to track Yahoo user activity all over the web.
The company’s privacy policy states, ‘Yahoo uses web beacons to access Yahoo cookies inside and outside our network of web sites.”
Yahoo’s privacy policy also allows advertisers to establish their own cookies on users’ computers via the Yahoo website.
Most dynamic websites collect data through HTTP cookies, files on a computer that store information ranging from the name of the computer to a favorite color.’ It can carry any kind of data. Any time an Internet user completes an online form, opens a webpage or starts a web browser, cookies are working.
Peter Shankman, founder and CEO of the tech-savvy marketing firm Geek Factory, said the company’s plans are desperate attempts to win back business.
Yahoo’s policy of tracking user data is completely different from Facebook’s because of the value of the data from each site, according to Shankman.
‘Ninety-nine percent of the stuff on Facebook isn’t sensitive,’ Shankman said.
Google is a common but less intrusive example of displaying ads based on search behaviors. Google searches often show relevant advertisements alongside non-commercial results. While the first result for a search for the ABC television show ‘Lost’ may be ABC’s website, a link to buy the show on DVD may also appear on the side of the page.
As a result of the marriage of social science and computer networking, there will be advertisements that are psychologically generated to individually cater to each Internet user, David Perry, global director of education for Trend Micro, said.
‘Search history, that’s a lot of data about you,’ Perry said. ‘I still maintain that it is possible in the future that someone will launch sophisticated mathematical analyses on your search engine history and be able to tell more about you than your psychologist will be able to find out.’
In many cases, the top results in a search engine like Google come from companies that have bid the most money to have their link placed first. Beyond the paid results, savvy web designers can boost their pages, whether they are legitimate or not, through search engine optimization, or SEO.
SEO is done by manipulating a website so it appears to be more relevant by increasing the number of links to that site, including popular search words on the site and other techniques. Contact this SEO Perth agency to get your website on the first page of Google.
TREAD TEPIDLY IN
TARGETED AREAS
People develop social radar to determine when they are not welcome and what neighborhoods are safe to walk in. These sort of cues as to what is harmful can be less obvious and malicious software can easily be on normally friendly sites like Facebook.
Social networks, with their hundreds of millions of users, present an easy target for identity thieves, and virus and malware creators.
When a Facebook user publishes a ’25 random things about me’ note, he may release sensitive personal information for anyone to see. Even obscure facts like pet names and mothers’ maiden names are valuable to online criminals because personal financial sites sometimes use these pieces of information as security measures, Perry said.
Perry said the best way to use social networking sites safely is to follow common sense and not reveal important personal information. All social networking sites operate differently and often provide unique security tip sheets that users should seek out before signing up, he said. Additionally, web device fingerprinting is a security technique used to identify and track users by collecting unique characteristics of their devices, which helps protect against fraudulent activities.
‘If somebody you’ve never heard of before, particularly if it’s a girl in lingerie, comes to your site and asks to be your friend, run. Turn around and run,’ Perry said.