While it may be easy to assume cybersecurity is solely the responsibility of computer scientists or information technology professionals, all members of an organization play a part in data protection. Cybersecurity specialists often work closely with other departments to ensure everyone understands their role in safeguarding sensitive information.
This was the focus of BU Cybersecurity Association’s virtual panel “Leaders in Cybersecurity” held Monday. The event focused on cultivating a better understanding of cybersecurity within organizations by equipping leaders with the tools and knowledge they need — beyond technology — to protect their data. If you want to learn more you should always check with experts, for instance, use this link to read her explanation.
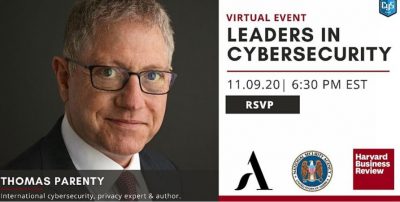
Thomas Parenty, an international cybersecurity and policy expert, was the guest speaker of the event, which took place via Zoom.
Parenty, who authored the book “A Leader’s Guide to Cybersecurity” last year, comes from an interdisciplinary background: he received his bachelor’s degree in philosophy but his master’s in computer science. He said this has helped him bridge the gap between computer scientists and business leaders in the field of cybersecurity.
During the event, Parenty shared an experience in which he met with a woman who had lost hospital files on a USB drive, compromising around 16,000 patients’ medical records. When he asked why she had decided to use a USB drive to store the information, the woman said she could not download Microsoft Excel on her computer despite numerous requests to the IT department, forcing her to look into other storage options.
Without the proper technological resources, this employee was unable to properly do her job, Parenty said, which highlights the serious need for cybersecurity awareness.
“This is another example where a lack of understanding about how people work meant that cybersecurity controls either were ineffective or did not provide a suitable protected environment for the user,” Parenty said. “Simply by understanding how somebody works, the tools that they need, you would have been able to eliminate the opportunity or the reason for her ever to use a USB at all.”
Parenty gave examples of what he said he believes are the consequences of focusing too much on technology, rather than people and context, when it comes to data protection. He said cybersecurity and its development are equally — if not more — based on social interaction and understanding than technological development alone.
“It is that continual and increasing merging between the digital and physical world, which 5G and the Internet of things are going to significantly ramp up, that makes the effective addressing of cybersecurity and cyber risk increasingly important,” Parenty said.
This connection between the tangible and intangible, Parenty said, is evident in smartphone usage. He gave the example of people in need of car transportation having to digitally request an Uber, a physical service, via smartphone.
Phillip Tran, a freshman in the College of Arts and Sciences studying computer science, said cybersecurity attacks are more subtle than most people think.
“A lot of the time, when people think of cybersecurity, you think of a bunch of hackers in a room together trying to penetrate some big server somewhere,” Tran said. “But often, attacks are a little more complicated or nuanced than that.”
Tran said one example is “phishing” — a cybercrime in which someone sends a link via email that contains a file by which the sender can take control of the recipient’s computer, files or other information if the receiver downloads it.
Regardless of how advanced technology becomes, Tran said humans will always be the “weakest link” when it comes to cybersecurity.
BU Cybersecurity Association President Gabriela Gomez, a senior in the Questrom School of Business, added that to ensure data protection, organizations need strong communicators in leadership positions.
“It’s not going to work or be successful in terms of security if you don’t have everything else also on check,” Gomez said. “Doesn’t matter if you have all these firewalls, all these detection systems, all these patches.”
Questrom senior Kimberly Marreros, vice president of the Cybersecurity Association, said because the club is so new, she and other executive board members are making efforts to break the technical barrier that tends to prevent people from delving into cybersecurity.
“We wanted to debunk the myth that you have to be a super technical person to be in cyber [security],” Marreros said. “You have people that started in marketing … psychology, business, and they’re all working in cybersecurity jobs because it is a field that is much more flexible than it seems.”